Setting up an ASA5505
Ok so another day, another piece of pre-loved Cisco equipment! This time, an ASA5505 which is going to be providing us with Firewall and port forwarding duties for our Lync environment.
First things first, quite easier to clear this and reset them so get to a prompt, go through all the usual security reset procedures you’ve learnt how to do in other posts, and enter the terminal configuration mode from an elevated prompt;
The above command will reset the device back to how it is from the factory with no configuration. Its important you get rid of the base configuration (even the bit Cisco provides when you purchase one) as most often than not, you won’t need these settings and they will just interfere with your install.
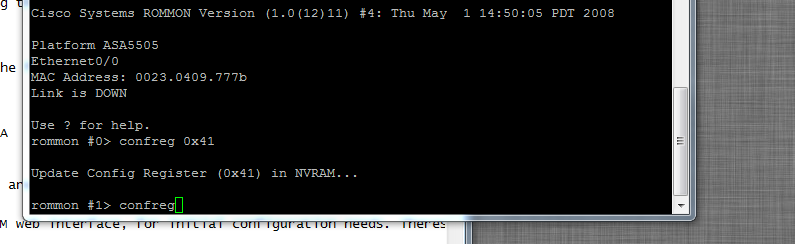
NB: If you find yourself getting stuck in a ROMMON prompt-shaped prison, you’ve possibly been trying to use configuration registers 0x2101 and 0x2142. Remember those guys? Well they won’t help you here, your after 0x41 on an ASA5505. Then enter the command boot and you’ll get a brand new config.
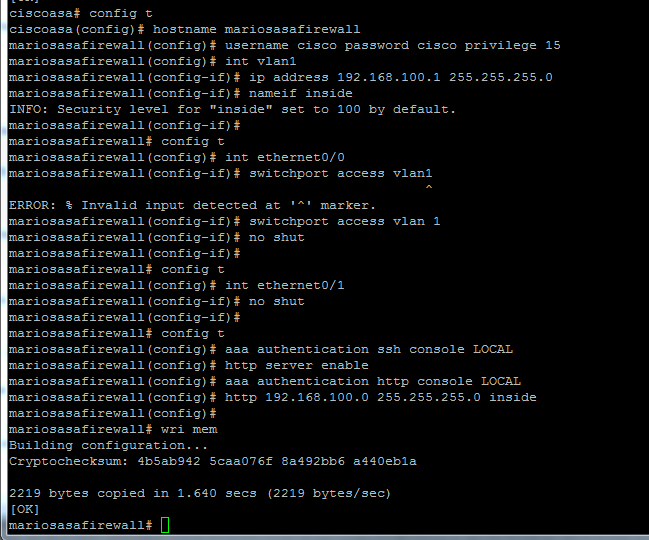
Initial Config & access via SSH and ASDM
So we need to set up the firewall to accept connections via SSH and ASDM (web GUI) using the following commands
Firstly, I set security (passwords here are dummies)
firewall(config)#username cisco password cisco privilege 15
Then I want to bring up the vlan1 interface which by default, all the other interfaces are bound to;
firewall(config)#int vlan1
firewall(config-if)#ip address 192.168.100.1 255.255.255.0
firewall(config-if)# nameif inside
Note the nameif command names the interface, and by default is set to the highest level of security, 100.
Then we need to bring up a couple of the ports. (NB port 0 is the accepted standard for the WAN entry and 1-7 are for LAN with ports 6 & 7 also having PoE capability)
firewall(config)# int ethernet0/0
firewall(config-if)# switchport access vlan 1
firewall(config-if)#no shut
Do the same for another port, but obviously no need to assign it to a vlan now.
Next we need to set SSH access availability using the local credentials we’ve set, so we use
firewall(config)# aaa authentication ssh console LOCAL
firewall(config)# http server enable
The command above allows access via ASDM and now we want to allow access for a specific IP range to access the ASDM
firewall(config)# aaa authentication http console LOCAL
firewall(config)# http 192.168.100.0.255.255.255.0 inside
It all looks like this;
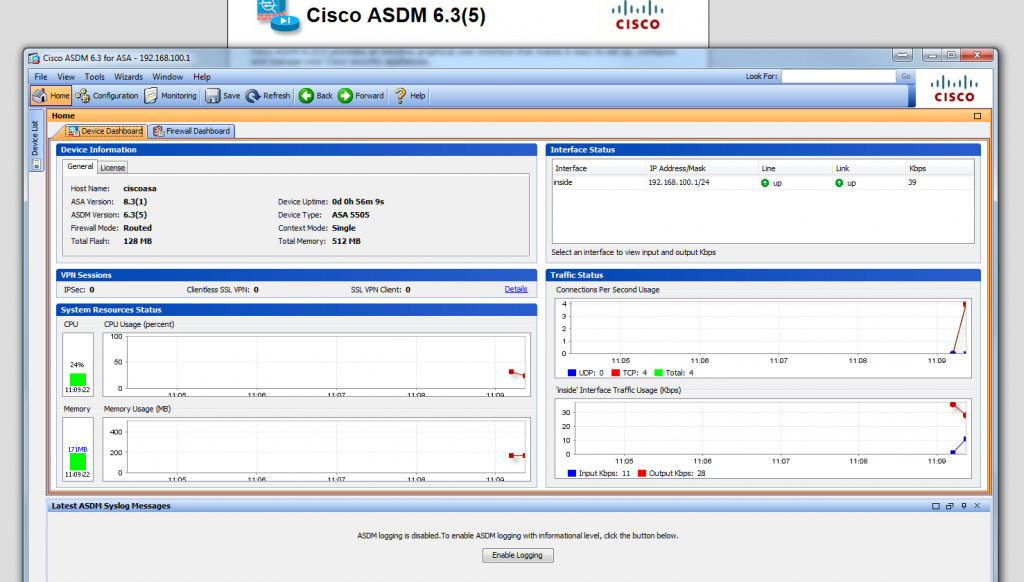
You can then start setting up the unit via SADSM which looks like this;
Problems with Faulty RAM
In the unit I have, it occasionally failed with a proprietary flashing of all the unit lights and halted the CLI, which is indicative of a faulty Flash or DIMM memory module. I used this website as a reference, but basically I just needed to reseat my existing RAM which had come loose. Anyway, if your interested, the inside looks like this;
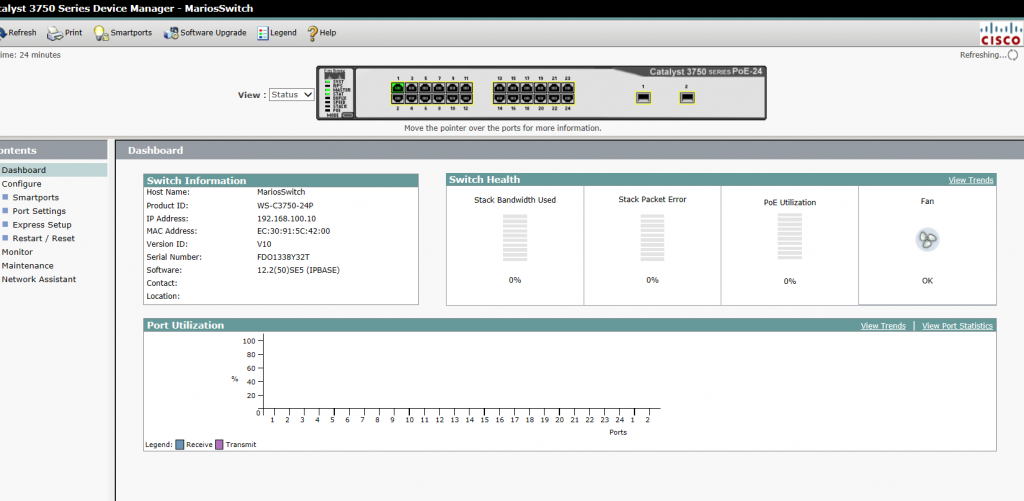
Our lab now looks like this